Segregation of Duties (SoD)
is a fundamental security and internal control principle designed to prevent the misuse, manipulation, or unauthorized alteration of systems and data. It does this by ensuring that no single individual has the ability to execute all critical steps within a sensitive business process. By distributing responsibilities across multiple roles or individuals, SoD helps create a system of checks and balances that significantly reduces the risk of fraud, errors, and unauthorized activities.
To enforce SoD, organizations divide key tasks among different roles and define strict access permissions that align with those responsibilities. For example, in a financial operation, the individual who prepares payroll entries must not be the same person who approves or authorizes payments. This separation ensures that even if one role is compromised, a malicious action cannot be completed without collusion, thereby strengthening both security and accountability.
SoD is widely recommended and upheld by major security and compliance frameworks such as NIST SP 800-53, ISO 27001, SOX (Sarbanes-Oxley Act), and COBIT. These frameworks emphasize SoD as a critical mechanism for maintaining operational transparency, ensuring regulatory compliance, and safeguarding organizational assets.
SoD in the Context of Role-Based Access Control (RBAC)
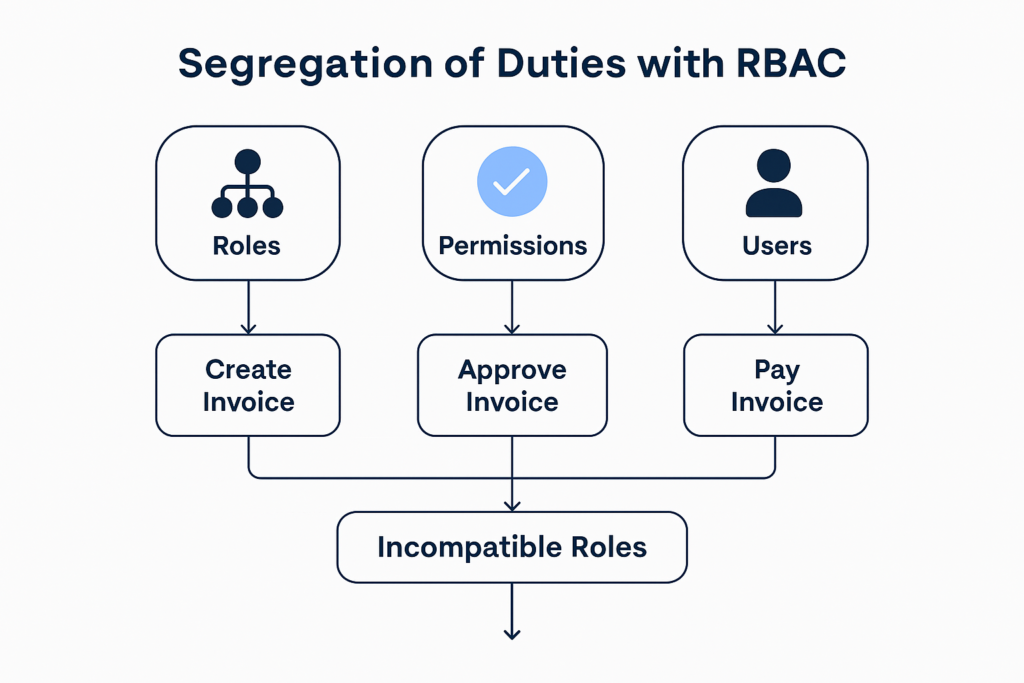
Within Role-Based Access Control (RBAC), SoD plays a central role in maintaining the integrity of business operations. RBAC assigns permissions based on predefined roles rather than individual users, making it easier to manage access rights consistently and to enforce SoD policies at scale.
SoD ensures that no single person holds end-to-end control over high‑risk activities. For example, when processing an invoice:
- One role may be responsible for creating or entering the invoice.
- Another role may validate or approve it.
- A third role may authorize and process the payment.
By distributing these tasks across distinct roles, organizations minimize the likelihood of fraud, unauthorized changes, or unintentional errors. RBAC simplifies this process by allowing administrators to restrict incompatible roles from being assigned to the same person. For instance, a user who holds the “Accountant” role should not simultaneously have the “Auditor” role, as this would create a conflict of interest and break SoD principles.
Implementing SoD within an RBAC framework requires:
- A detailed understanding of business processes, workflows, and the relationships between tasks.
- Identification of sensitive functions and the risks associated with them.
- Definition of “toxic combinations” of roles that should not be assigned to a single user.
- Ongoing monitoring to detect violations, ensure compliance, and adjust controls as business needs evolve.
When properly implemented, SoD combined with RBAC provides a robust, scalable security model that enhances trust, reduces operational risks, and supports regulatory compliance across the organization.
